Information SEcurity > Introduction to Security > Information Security Programs
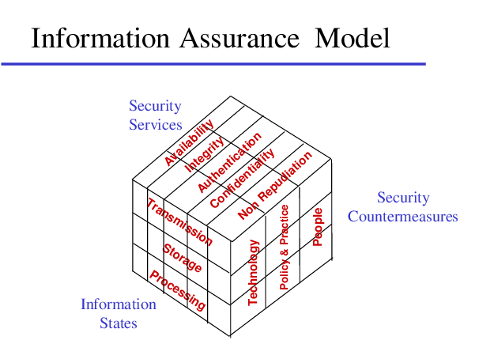
Information assurance
The ongoing process of achieving confidentiality, integrity and availability of data within an information system is known as “information assurance.”
Information Security Programs
An Information Security Program is a structured set of policies, procedures, and controls that are designed to protect an organization’s digital and physical information assets from unauthorized access, disclosure, alteration, or destruction. It ensures the confidentiality, integrity, and availability (CIA triad) of data.
Key Components of an Information Security Program Risk Management:
Risk management involves identifying, assessing, and managing risks to information systems and data. For example, organizations conduct regular vulnerability assessments to identify potential weaknesses.
Security Policies and Procedures: Security policies and procedures are documented rules and guidelines that define how information assets must be handled. For example, organizations implement password policies and acceptable use policies to guide users.
Access Control: Access control ensures that only authorized users can access specific data or systems. For example, role-based access control (RBAC) is used to assign permissions based on user roles.
Authentication and Authorization: Authentication and authorization involve verifying user identities and granting appropriate access rights. For example, organizations use two-factor authentication (2FA) to enhance security.
Incident Response Plan: An incident response plan defines the steps required to detect, respond to, and recover from security breaches. For example, organizations maintain a detailed procedure for handling ransomware attacks.
Security Awareness Training: Security awareness training involves educating employees about best practices and common security threats, such as phishing. For example, many organizations require mandatory annual cybersecurity training for employees.
Data Encryption and Protection: Data encryption and protection involve using encryption techniques to secure sensitive data both in transit and at rest. For example, customer data stored in databases is often encrypted. Monitoring and Auditing: Monitoring and auditing involve continuously observing systems and conducting periodic reviews to detect suspicious activities. For example, organizations log and review user activities on networks.
Compliance and Legal Requirements: Compliance and legal requirements involve adhering to relevant laws, regulations, and standards such as GDPR and ISO/IEC 27001. For example, organizations ensure that their data privacy practices align with legal frameworks.
Feedback
ABOUT
Statlearner
Statlearner STUDY
Statlearner