Information SEcurity > Introduction to Security > What is CIA Triad?
CIA Triad
The CIA Triad is a fundamental model in information security that focuses on three key principles. First suggested by the National Institute of Standards and Technology (NIST) in 1977, the CIA triad is intended to guide organizations in choosing technologies, policies and practices to protect their information systems. The elements of the CIA triad include:
- Confidentiality
- Integrity
- Availability

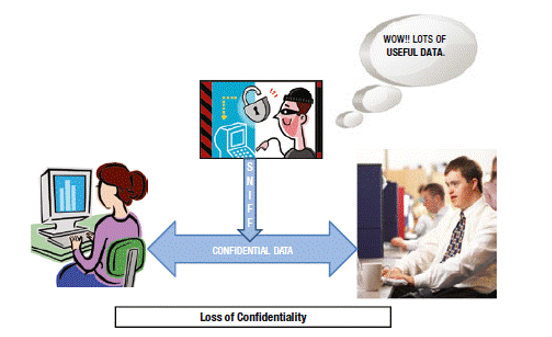
Confidentiality: Confidentiality means ensuring that parties cannot access data they're not authorized to access. There are different levels of users:
- Privileged users → can access most company data (e.g., admin)
- Limited users → can access only specific data
- Public users → can access only publicly available information
Sensitive and personal data must always remain private and protected and confidentiality defines privileged of all types of users. Personal information should remain private. Sensitive data is sensitive. If an unauthorized person obtains a password to protected data, it would be a confidentiality breach.
Example:
- A student cannot see another student’s grades
- Only authorized staff can access confidential reports
Integrity: Integrity focuses on maintaining the correctness and consistency of data in a system. It ensures that:
- Data is not tampered with
- No unauthorized additions, changes, or deletions occur
- Information remains reliable and trustworthy
Integrity protects against:
- Malicious users (attackers) who intentionally change data
- Authorized users who may accidentally or improperly modify data
Example: Bank balance should not change without a valid transaction
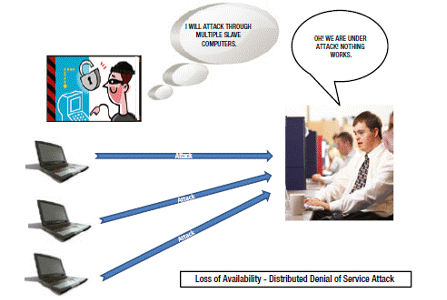
Availability
Availability means ensuring that users can access the information they're authorized to access when they need it. Availability dictates that information security measures and policies should not interfere with authorized data access. Much of availability is straightforward, such as working to ensure the robustness of hardware and software to prevent an organization’s sites going down.
Nonrepudiation
Nonrepudiation ensures that a user cannot deny having performed a specific action—such as sending a message or modifying data—because the action required authentication to take place. Although it is not formally part of the CIA triad (Confidentiality, Integrity, Availability), nonrepudiation is closely related to both confidentiality and integrity. It guarantees that only authorized users can access or modify data, and that their actions are securely recorded, preventing them from later denying their involvement.
Example: A manager logs into a company’s financial system using their unique ID and password, then approves a large fund transfer to a vendor. The system records the transaction with a digital signature and timestamp, tied to the manager’s identity.
Later, if the manager tries to deny authorizing the transaction, the system's authentication logs and digital signature serve as proof that the action was performed by them. This ensures nonrepudiation—they cannot deny it
Authentication
Authentication is the process of verifying the identity of a user, device, or system before granting access to resources or services. It ensures that the entity requesting access is truly who it claims to be. Authentication is a key part of information security and is commonly based on one or more of the following:
- Something you know (e.g., password or PIN)
- Something you have (e.g., ID card, smartphone, security token)
- Something you are (e.g., fingerprint, face, or other biometrics)
Example: A student wants to access their university portal to check exam results. To log in, they:
- Enter their student ID and password (something they know).
- Receive a one-time code (OTP) on their registered mobile phone (something they have).
- Optionally, scan their fingerprint if biometric authentication is enabled (something they are).
- Once verified, the system grants access. This process ensures the person logging in is the legitimate student.
Feedback
ABOUT
Statlearner
Statlearner STUDY
Statlearner